Getting Started
How to get started with Cobalt.
Visualize your journey with Cobalt, and launch your first pentest to make your security stronger.
Take your first steps to get started:
Prepare for a Pentest
Pentest Preparation Checklist »
- Make your teams aware of the upcoming pentest.
- Notify everyone who should be aware of the pentest. Ensure that the pentest doesn’t disrupt anyone’s workflows.
- Prepare credentials and account details for pentesters.
- Be responsive to pentest results.
- Be available to help find solutions to problems.
- Most of the time pentesters are cautious and don’t perform any actions that have detrimental effects on your software. However, as a precautionary measure, you should prepare for the worst. Prepare a backup copy of your software (especially when testing a production environment), and have a team ready to respond to any unexpected events.
- Establish communication with pentesters in Slack, and let them know you are there—available and responsive.
- Communicate significant changes to your environment made during a test to pentesters.
- If you make significant changes to your environment during a test (including remediating vulnerabilities), make sure to communicate this to our pentesters. Any major updates to your asset that you make when the pentest is Live may impact pentesters’ workflows and the testing process.
Launch a Pentest
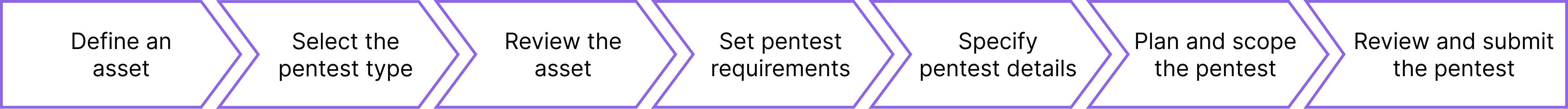
Sign in to Cobalt, and start with defining your assets. Here are the steps you need to take.
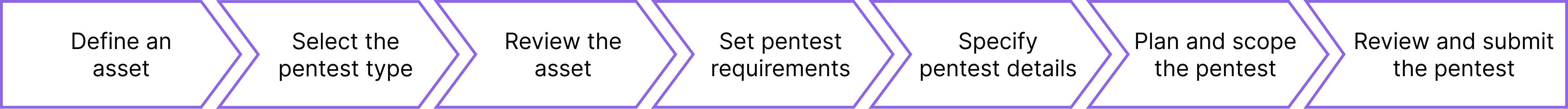
Click to learn more.
- Define your assets. Our pentesters analyze all kinds of
assets, from web apps to internal networks.
- Select the pentest type. We offer Agile and Comprehensive Pentests.
- Review your asset.
- Set requirements for your pentest.
- Define details of your environment.
Is your asset in production or in development? Is part of your system
on a Cloud platform?
- Plan and scope the test. Define your desired pentest start
date, and specify the pentest scope. We need time to find the best available pentesters for your assets.
- Review your pentest request to make
sure you’ve included all information that our pentesters need.
Once you’ve set up a pentest, we start analyzing your asset. When
possible, we share results even before we create your report. Here’s what
you can expect.
Frequently Asked Questions
Click to view answers.
What is an organization?
When you receive an email invitation from Cobalt, you join a specific organization with a role assigned to you. Within an organization, you and your team get access to the Cobalt platform and the pentest experience. Learn more about
organizations.
How do I add people to my organization?
Organization Owners can manage users for their organization. For instructions, see
Invite Users.
What is an asset?
For pentests, an asset is a software component of value, such as a web application or API. Learn more about the
asset types we support. Once you've created an asset, you can launch pentests for it.
Get in Touch
If you need help, don’t hesitate to contact us.
We process support requests within one business day.
If you find a security issue on the Cobalt platform, please report it to security@cobalt.io. Learn more about our security practices.
Information needed to set up your pentest.
Start the pentest process. Sign in to the Cobalt app.
Security professionals perform pentests on your assets. Collect the info they need.
Start setting up your pentest.
Set requirements for the pentest.
Describe key details of your pentest.
Set up a schedule. Scope the pentest.
Review your pentest request.
What happens after you’ve set up your pentest.
Learn more about the language of software security.
Last modified June.06.2023